Overview of CVE-2025-11953
CVE-2025-11953 describes an operating system (OS) command injection vulnerability identified in the React Native Community CLI, a development tool maintained by the React Native Community. The CLI is commonly used by developers to initialize, configure, and manage React Native projects during local development and build processes.
At the time of writing, public technical details are limited. Based on the vulnerability classification, the issue likely arises from insufficient input validation or improper sanitization when user-supplied or environment-derived input is passed to underlying shell commands.
Affected Products and Versions
Product: React Native Community CLI
Component: CLI command handling and execution logic
Affected Versions:
Specific affected versions have not yet been conclusively listed in public advisories. Until vendor guidance is published, users should assume that multiple recent releases may be impacted, particularly those that invoke system commands based on project configuration, parameters, or templates.
Organizations are advised to monitor official disclosures from the maintainers and the National Vulnerability Database (NVD) for confirmed version ranges.
Technical Impact and Risk
If successfully exploited, this vulnerability could allow an attacker to execute arbitrary OS-level commands in the context of the user running the CLI. In typical development environments, this may result in:
Unauthorized command execution on developer workstations or CI/CD runners
Modification or deletion of source code and build artifacts
Exposure of sensitive environment variables or credentials
Lateral movement within internal development infrastructure
While exploitation generally requires some level of access—such as the ability to influence CLI inputs or configuration files—the impact can be significant, especially in automated pipelines.
Proof of Concept (High-Level)
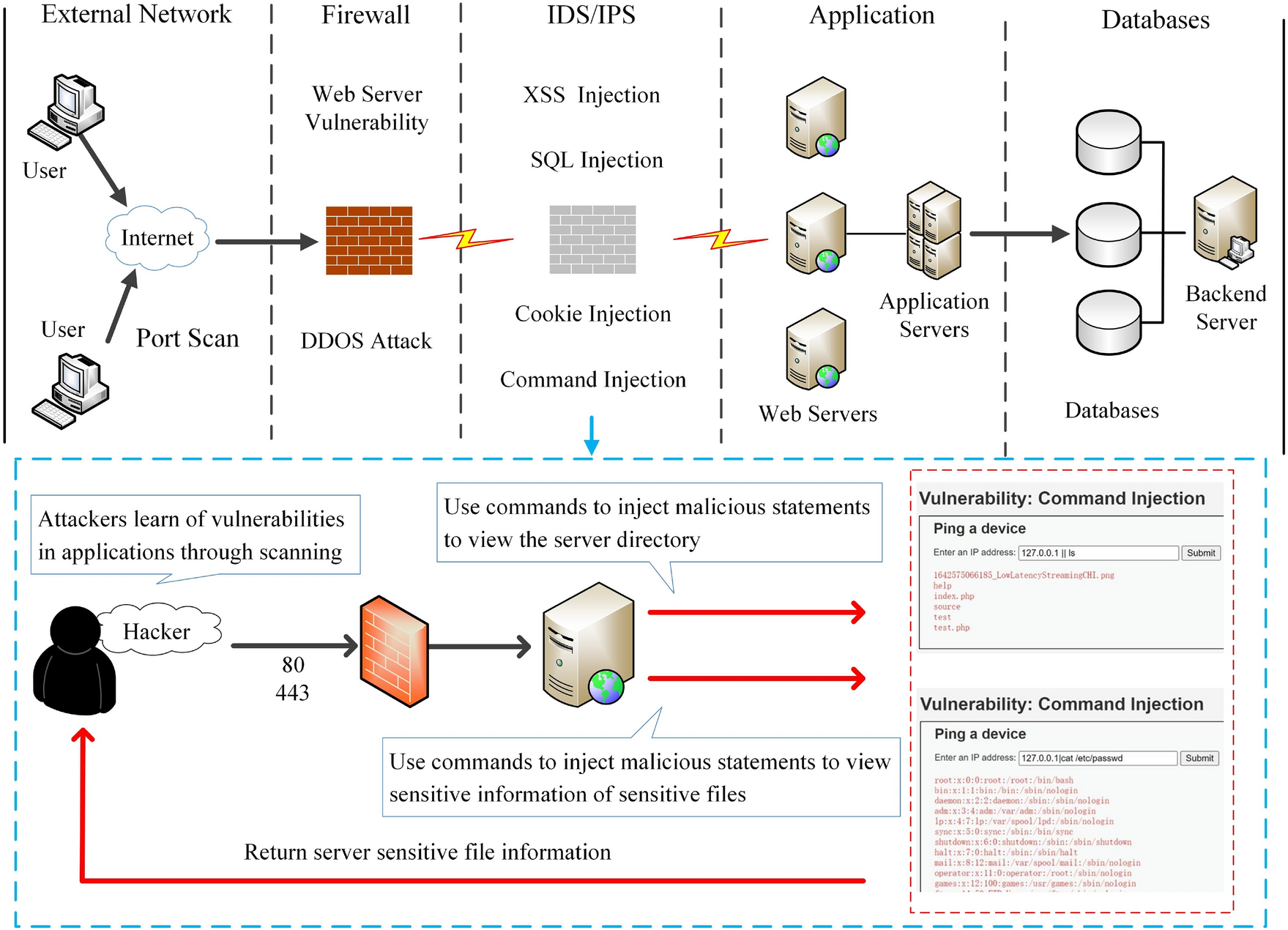
At a high level, an OS command injection scenario for a CLI tool typically involves:
The CLI accepting user-controlled input (for example, a project name, path, or configuration value)
That input being concatenated into a system command without adequate sanitization
The underlying operating system shell interpreting the injected characters as additional commands
This description is intentionally non-operational and omits exploit details to avoid misuse.
Mitigation and Remediation Guidance
Until an official patch or advisory is released, the following defensive measures are recommended:
Update promptly once a fixed version of the React Native Community CLI becomes available
Restrict usage of the CLI in untrusted environments or where inputs may be externally influenced
Review CI/CD pipelines to ensure that build jobs do not process untrusted configuration or parameters
Apply the principle of least privilege, ensuring the CLI runs with minimal OS permissions
Monitor developer systems for anomalous command execution or unexpected file changes
Security teams should also consider compensating controls such as endpoint protection and command-line auditing.